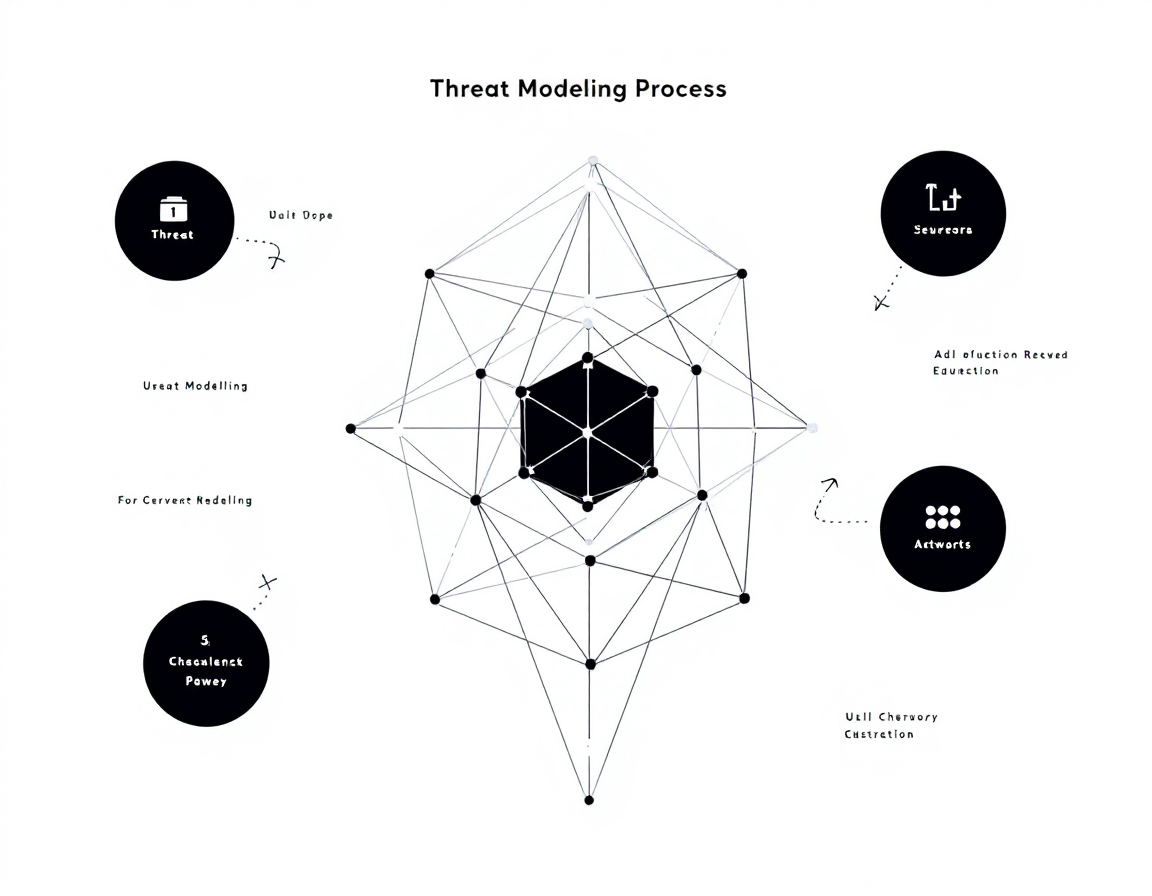
The Threat Modeling Process
Threat modelling isn’t optional anymore—it’s how security teams stay ahead of attackers. This course walks you through the structured process of identifying, analysing, and prioritising threats before they become incidents. You’ll leave with a repeatable framework you can apply immediately to your organisation’s systems.
AIU.ac Verdict: Ideal for security engineers, architects, and developers who need to embed threat analysis into their workflow without weeks of study. The 56-minute format is a genuine strength for busy teams, though it’s an introduction rather than an exhaustive deep-dive into advanced attack scenarios.
What This Course Covers
The course covers the core threat modelling methodology: scoping your system, identifying potential threats, analysing their impact and likelihood, and prioritising remediation efforts. You’ll work through real-world examples that demonstrate how to map data flows, spot trust boundaries, and recognise common attack vectors—the practical mechanics that separate theoretical security from actionable defence.
Peter Mosmans brings hands-on experience to each concept, showing you how threat modelling fits into the broader security development lifecycle. The labs and sandboxes let you apply the process directly, building confidence in your ability to lead threat modelling sessions and communicate findings to stakeholders.
Who Is This Course For?
Ideal for:
- Security engineers and architects: Need a structured, repeatable process to assess systems before deployment and during design reviews.
- Developers and tech leads: Want to shift security left by understanding threats early, reducing costly fixes later in the pipeline.
- Security analysts and compliance teams: Require a systematic approach to document threat landscapes and justify security investments to leadership.
May not suit:
- Absolute beginners to cybersecurity: Assumes baseline knowledge of systems architecture, data flows, and common attack types. Start with foundational security courses first.
- Specialists seeking advanced threat modelling frameworks: Covers fundamentals well but doesn’t deep-dive into STRIDE, PASTA, or other formal methodologies in granular detail.
Frequently Asked Questions
How long does The Threat Modeling Process take?
56 minutes of video content. Most learners complete it in one sitting or across two focused sessions, making it ideal for busy professionals.
Do I need prior cybersecurity experience?
You should understand basic systems architecture and networking concepts. If you’re new to security entirely, consider a foundational course first.
Will this teach me specific frameworks like STRIDE or PASTA?
The course covers the threat modelling process and principles. It introduces you to the methodology; deeper framework training is available in specialist follow-up courses.
Can I apply this immediately in my role?
Yes. The hands-on labs and practical examples give you a framework to use in your next design review or security assessment.
Course by Peter Mosmans on Pluralsight. Duration: 0h 56m. Last verified by AIU.ac: March 2026.