Protecting Sensitive Data From Exposure in ASP.NET 3 and ASP.NET Core 3 Applications
Data breaches cost organisations millions—and your ASP.NET applications are prime targets if you’re not hardening them properly. This course cuts through the noise to show you exactly how to prevent sensitive data exposure in production environments, covering encryption, secure storage, and defensive coding patterns you’ll use immediately.
AIU.ac Verdict: Essential for backend developers and security-conscious architects building ASP.NET applications handling PII, payment data, or regulated information. You’ll gain hands-on patterns from a Pluralsight-vetted expert, though the 92-minute runtime means this is focused depth rather than exhaustive coverage—pair it with ongoing threat modelling for enterprise-scale systems.
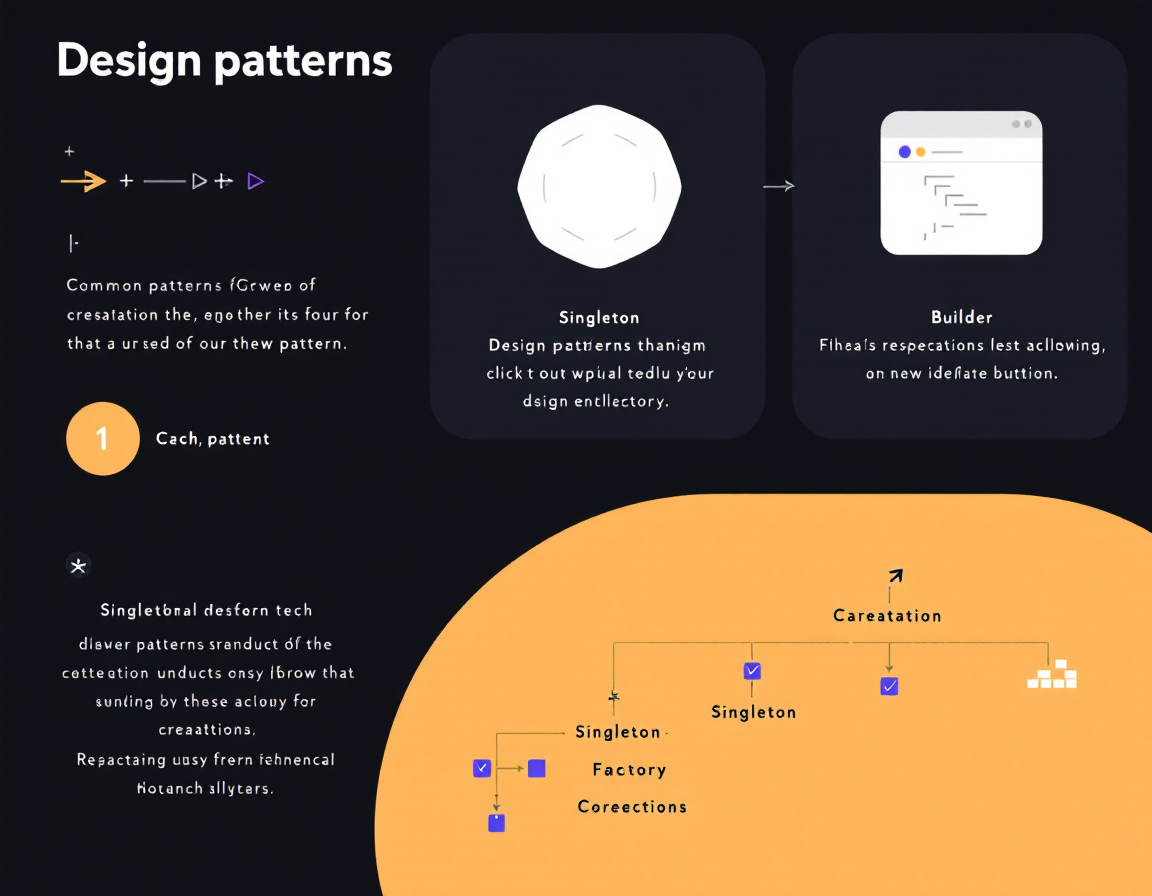
What This Course Covers
You’ll work through real-world scenarios: encrypting data at rest and in transit, managing secrets safely outside your codebase, preventing common injection attacks, and implementing secure authentication flows specific to ASP.NET 3 and Core 3 frameworks. The course emphasises practical code patterns you can refactor into existing projects without architectural rewrites.
Matt Tester walks you through configuration hardening, secure session management, and protecting sensitive fields in logs and error messages—the gaps where breaches actually happen. Pluralsight’s sandbox labs let you test each pattern immediately, so you’re not just watching; you’re building muscle memory for security-first development.
Who Is This Course For?
Ideal for:
- ASP.NET backend developers: Building APIs or web applications that handle customer data, payments, or regulated information. You need immediate, framework-specific patterns.
- Security-conscious architects: Reviewing or upgrading legacy ASP.NET systems to meet compliance requirements (GDPR, PCI-DSS). This course bridges the gap between security theory and .NET reality.
- Tech leads and code reviewers: Responsible for catching data exposure vulnerabilities before production. You’ll gain the knowledge to mentor teams and set security standards.
May not suit:
- Absolute beginners to ASP.NET: You’ll need solid C# and HTTP fundamentals first. This assumes you’re already shipping ASP.NET code.
- DevOps or infrastructure-focused engineers: The course is application-layer security, not network hardening or cloud infrastructure patterns.
Frequently Asked Questions
How long does Protecting Sensitive Data From Exposure in ASP.NET 3 and ASP.NET Core 3 Applications take?
1 hour 32 minutes. It’s designed for focused learning—expect to complete it in one or two sittings, with time to practise the labs.
Will this cover ASP.NET 5+ or just 3 and Core 3?
The course focuses on ASP.NET 3 and ASP.NET Core 3. Core security patterns transfer forward, but check Pluralsight’s newer releases if you’re on .NET 6+.
Do I get hands-on labs or just video lectures?
Pluralsight includes interactive sandbox labs alongside video instruction, so you’ll code along with Matt Tester and test patterns in real environments.
Is this enough to pass security certifications?
It’s excellent foundational knowledge for application security, but certification paths (CISSP, CEH) require broader study. Use this as a core component of your prep.
Course by Matt Tester on Pluralsight. Duration: 1h 32m. Last verified by AIU.ac: March 2026.